What is TFlower Ransomware?
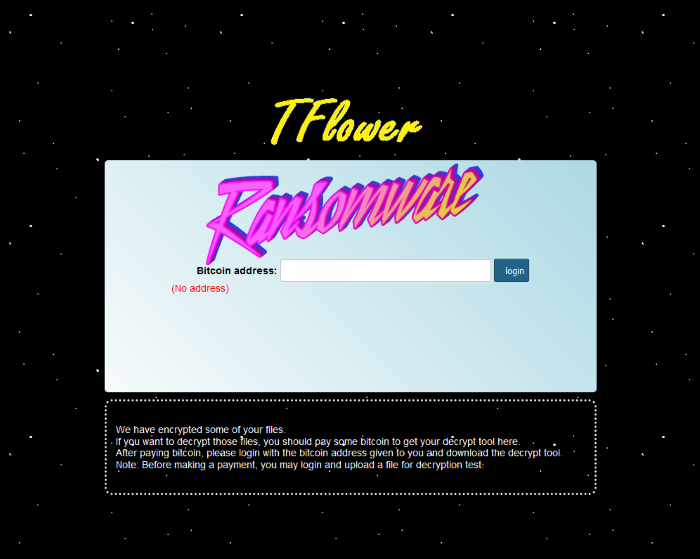
When your files become unreadable and it seems that nothing has changed, the reason of it can be TFlower Ransomware and you should remove it as soon as possible. TFlower belongs to the encryption viruses family, it means, that such a malware changes the structure of a file and it requires a special key to reverse this process. Usually, after encryption files get an appendix, but in our case nothing changes, as encryption proceeds according to the algorithm of Cipher Block Changing. In any case, it requires a special key to decrypt your files. TFlower ransomware attacks are aimed to different types of companies, but there is always a chance for a private citizen to be infected. When decryption process is done, you will receive a ransom note from the hackers. It usually places somewhere in a visible place. Usually hackers try to intimidate, or to relax you, in order to make you pay as soon as possible. Let’s have a look at TFlower’s note:
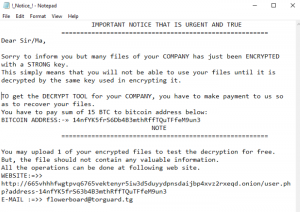
IMPORTANT NOTICE THAT IS URGENT AND TRUE
==============================================
Dear Sir/Ma,
Sorry to inform you but many files of your COMPANY has just been ENCRYPTED with a STRONG key.
This simply means that you will not be able to use your files until it is decrypted by the same key used in encrypting it.
TO get the DECRYPT TOOL for your COMPANY, you have to make payment to us so as to recover your files.
You have to pay sum of 15 BTC to bitcoin address below:
BITCOIN ADDRESS:-» *address*
NOTE
=============================================
You may upload 1 of your encrypted files to test the decryption for free.
But, the file should not contain any valuable information.
All the operations can be done at following web site.
WEBSITE:=>>
*address*
E-MAIL :=>> *e-mail*
As you can see, hacker tries to make you feel comfortable, he says that there is nothing to worry about. We strongly advice you not to pay intruders! There is no a guarantee, that he will honor his promise and restore your files. If you want to remove TFlower Ransomware and decrypt .exe files, read our guide!
Article’s Guide
- How to remove TFlower Ransomware from your computer
- How to remove TFlower Ransomware encryption from your files
- Data Recovery
- Automated decryption tools
- Windows Previous Versions
How to remove TFlower Ransomware from your computer?
We strongly recommend you to use a powerful anti-malware program that has this threat in its database. It will mitigate the risks of the wrong installation, and will remove TFlower from your computer with all of its leftovers and register files.
Solution for Windows users: our choice is Norton 360 . Norton 360 scans your computer and detects various threats like TFlower, then removes it with all of the related malicious files, folders and registry keys.
If you are Mac user, we advise you to use Combo Cleaner.
How to remove TFlower Ransomware encryption from your files?
Once you’ve removed the virus, you are probably thinking of recovering files from encryption. Let’s take a look at possible ways of decrypting your data.
Recover data with Data Recovery

- Download and install Data Recovery
- Select drives and folders with your files, then click Scan.
- Choose all the files in a folder, then press on Restore button.
- Manage export location.
Restore data with automated decryption tools
Unfortunately, due to the novelty of TFlower ransomware, there are no available automatic decryptors for this encryptor yet. Still, there is no need to invest in the malicious scheme by paying a ransom. You are able to recover files manually.
You can try to use one of these methods in order to restore your encrypted data manually.
Restore data with Windows Previous Versions
This feature is working on Windows Vista (not Home version), Windows 7 and later versions. Windows keeps copies of files and folders which you can use to restore data on your computer. In order to restore data from Windows Backup, take the following steps:
- Open My Computer and search for the folders you want to restore;
- Right-click on the folder and choose Restore previous versions option;
- The option will show you the list of all the previous copies of the folder;
- Select restore date and the option you need: Open, Copy and Restore.
Restore the system with System Restore
You can always try to use System Restore in order to roll back your system to its condition before infection infiltration. All the Windows versions include this option.
- Type restore in the Search tool;
- Click on the result;
- Choose restore point before the infection infiltration;
- Follow the on-screen instructions.