What is Termit?
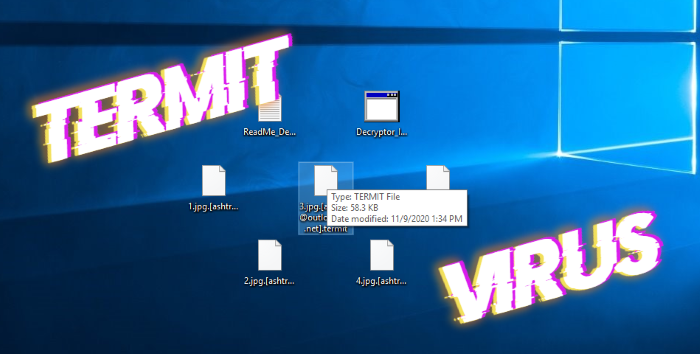
Nowadays, the internet is a very useful tool to perform a great variety of tasks. With its help we can do our job, study, chat or just have fun. However, it’s not safe. Every day criminals force thousands of people to pay. In order to do it, they create new viruses and other threats. Among them is Termit ransomware. This virus doesn’t belong to any already known file-encryption ransomware family and is not very widespread nowadays, but it can easily become the most widespread one. It’s possible because of the ways hackers use to spread it. In the most cases they use fake installers to do it. You can easily download such files from various free file sharing services and torrent trackers. As the rule, they are promoted as free software or updates for Flash Player. When Termitgets into the operating system, it modifies some registry keys and then infects system processes. By the means of them, Termit virus encrypts your files. As the result of it, your files get new “.[ashtray@outlookpro.net].termit” extension. At the same time Termit drops the ransom notes called “ReadMe_Decryptor.txt” and “Decryptor_Info.hta”. The purpose of these notes is to force victims to purchase hackers’ decryption services. We strongly recommend you to avoid any contact with them. Generally, hackers just ignore victims after the payment, make them pay twice, or even infect their devices with another virus. Moreover, the price is too high. And still there is a possible way out. Read our detailed guide on how to remove Termit ransomware and decrypt “.[ashtray@outlookpro.net].termit” files without paying ransoms!

Ransom note
Warning!
For decryption write here - : ashtray@outlookpro.net (Write only in English)
If you do not receive an answer write here - askebeger@protonmail.com
Jabber contact for online communication (not always available, but I will answer as I see) - askebeger@xmpp.jp (xmpp.jp - registration, web client - https://web.xabber.com )
Don't modify the files - you will ruin them. Test decryption < 500 kb (not databases and important files, only for demonstration of decryption)
[/expand]
Article's Guide
- How to remove Termit ransomware from your computer
- Automatically remove Termit ransomware
- Manually remove Termit ransomware
- How to decrypt .Termit files
- Automatically decrypt .Termit files
- Manually decrypt .Termit files
- How to prevent ransomware attacks
- Remove Termit ransomware and decrypt .Termit files with our help
How to remove Termit ransomware from your computer?
Every day ransomware viruses change as well as their folders, executable files and the processes, which they use. For this reason it's difficult to detect the virus yourself. That's why we've prepared the detailed guide for you on how to remove Termit ransomware from your computer!
Automatically remove Termit ransomware
We strongly recommend you to use automated solution, as it can scan all the hard drive, ongoing processes and registry keys. It will mitigate the risks of the wrong installation and will definitely remove Termit ransomware from your computer with all of its leftovers and register files. Moreover, it will protect your computer from future attacks.
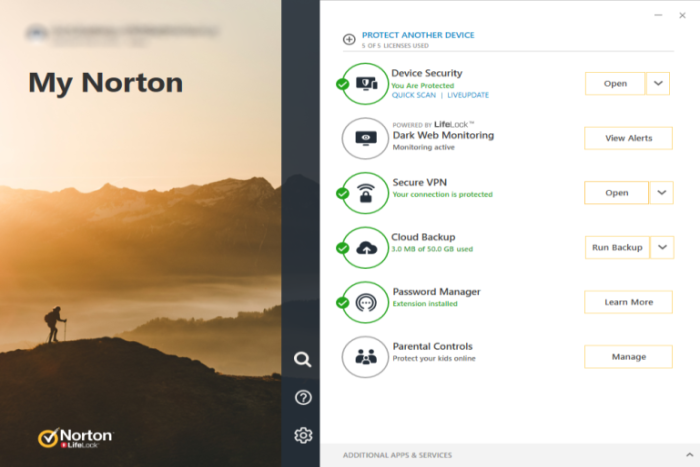
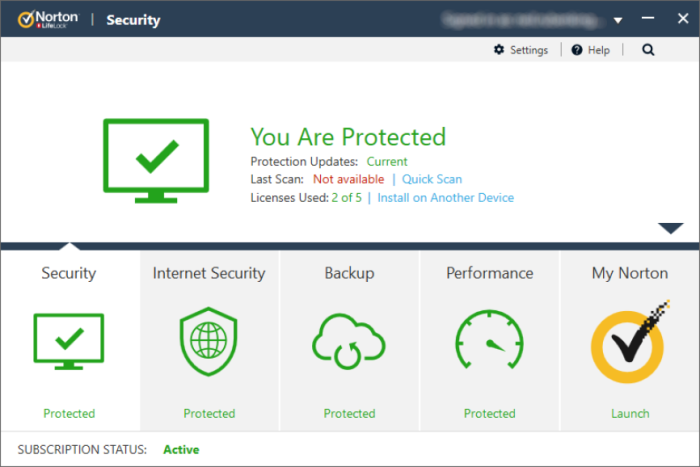
Our choice is Norton 360 . Norton 360 scans your computer and detects various threats like Termit virus, then removes it with all of the related malicious files, folders and malicious registry keys. Moreover, it has a great variety of other features, like protection from specific ransomware attacks, safe box for your passwords and many other things!

Manually remove Termit ransomware
This way is not recommended, as it requires strong skills. We don't bear any responsibility for your actions. We also warn you that you can damage your operating system or data. However, it can be a suitable solution for you.
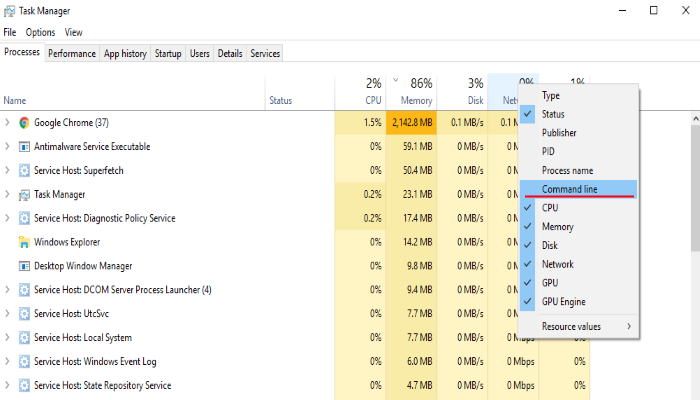
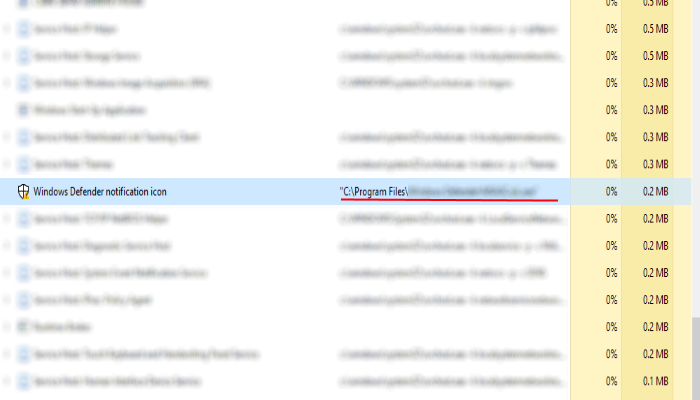
- Open the "Task Manager"
- Right click on the "Name" column, add the "Command line"
- Find a strange process, the folder of which probably is not suitable for it
- Go To the process folder and remove all files
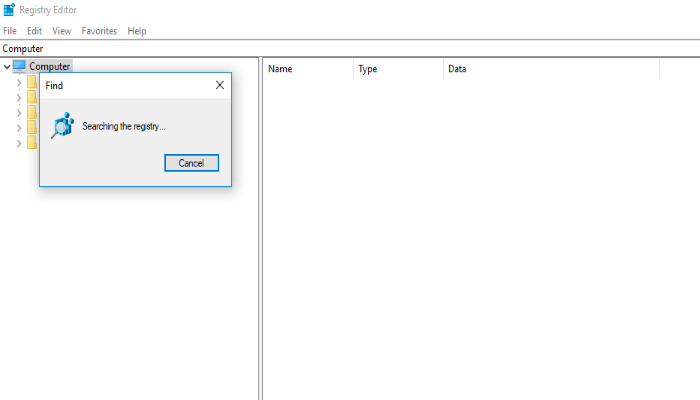
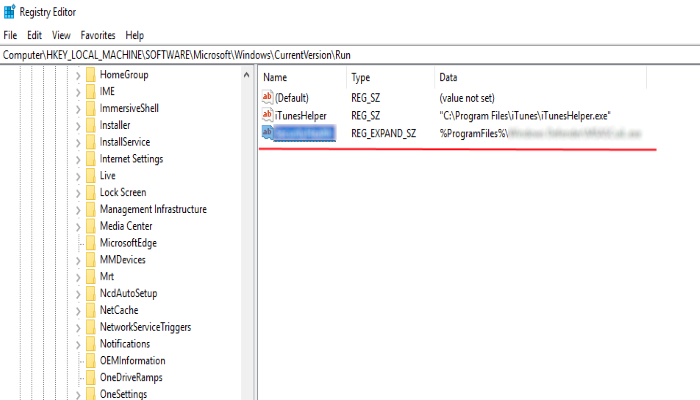
- Go to the Registry and remove all keys related to the process
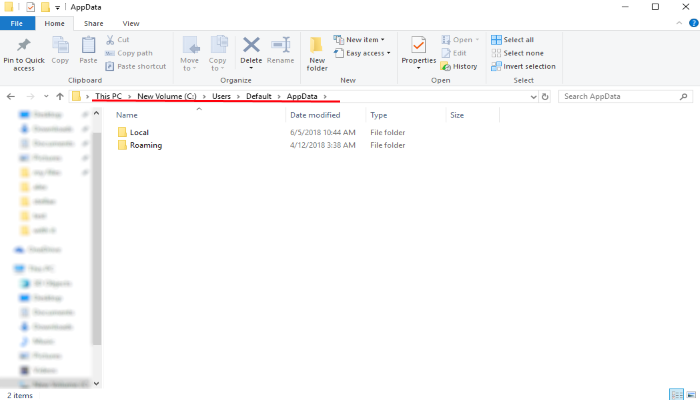
- Go to the AppData folder and remove all strange folders, that you can find
How to decrypt .Termit files?
Once you’ve removed the virus, you are probably thinking how to decrypt ".Termit" files or at least restore them. Let’s take a look at possible ways of decrypting your data.
Restore .Termit files with Stellar Data Recovery
If you decided to recover your files, we strongly advise you to use only high-quality software, otherwise your data can be corrupted. Our choice is Stellar Data Recovery. This software has proven to be very appreciated by customers, who have faced ransomware problems!

- Download and install Stellar Data Recovery
- Select drives and folders with your files, then click Scan.
- Choose all the files in a folder, then press on Restore button.
- Manage export location.
The download is an evaluation version for recovering files. To unlock all features and tools, purchase is required ($49.99-299). By clicking the button you agree to EULA and Privacy Policy. Downloading will start automatically.
Other solutions
The services we've mentioned in this part also guarantee users, that the encrypted data is unlikely to become damaged. But you should understand, that there is still a risk to corrupt your files.
Decrypt .Termit files with Emsisoft decryptor
.termit files"] This software includes information about more than 100 viruses of STOP(DJVU) family and others. All that you need are two files or some luck. You can freely use it as it distributes free of charge. If it doesn't work for you, you can use another method.Decrypt .Termit files with Kaspersky decryptors
Decrypt .Termit files with Dr. Web decryptors
Decrypt .Termit files manually
If above mentioned solutions didn't help to decrypt .Termit files, still, there is no need to invest in the malicious scheme by paying a ransom. You are able to recover files manually.
You can try to use one of these methods in order to restore your encrypted data manually.
Restore .Termit files with Windows Previous Versions
- Open My Computer and search for the folders you want to restore;
- Right-click on the folder and choose Restore previous versions option;
- The option will show you the list of all the previous copies of the folder;
- Select restore date and the option you need: Open, Copy and Restore.
Restore .Termit files with System Restore
- Type restore in the Search tool;
- Click on the result;
- Choose restore point before the infection infiltration;
- Follow the on-screen instructions.
How to prevent ransomware attacks?
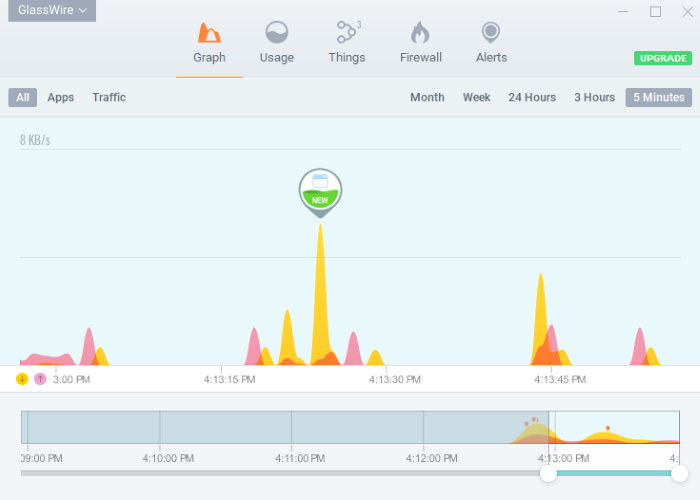
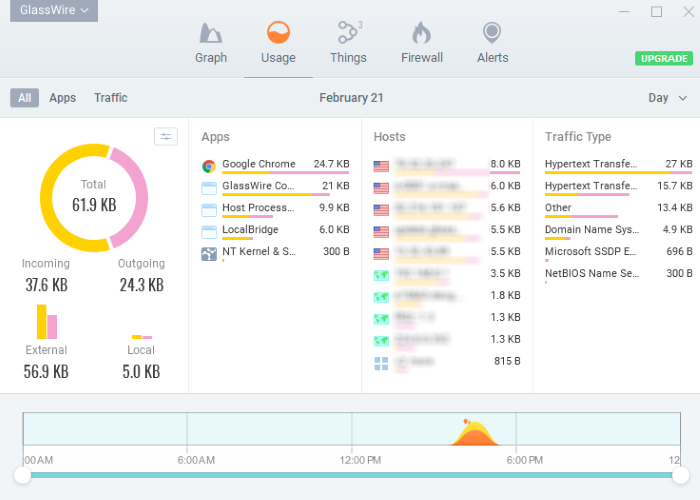
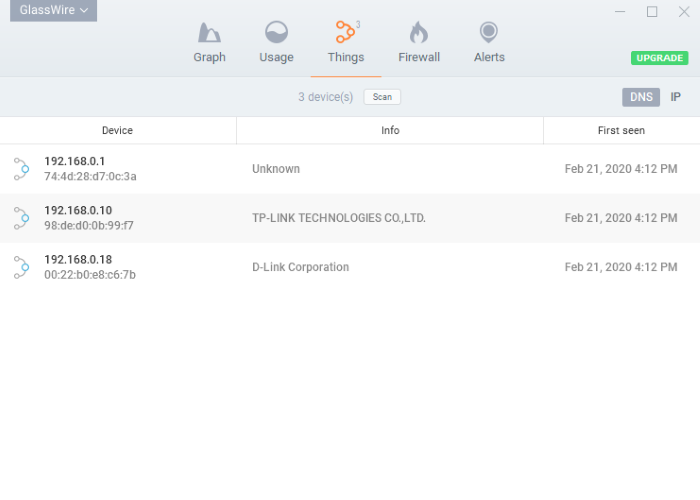
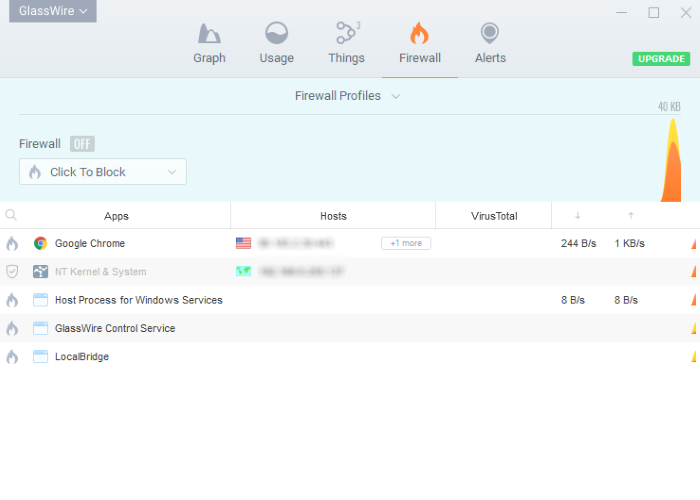
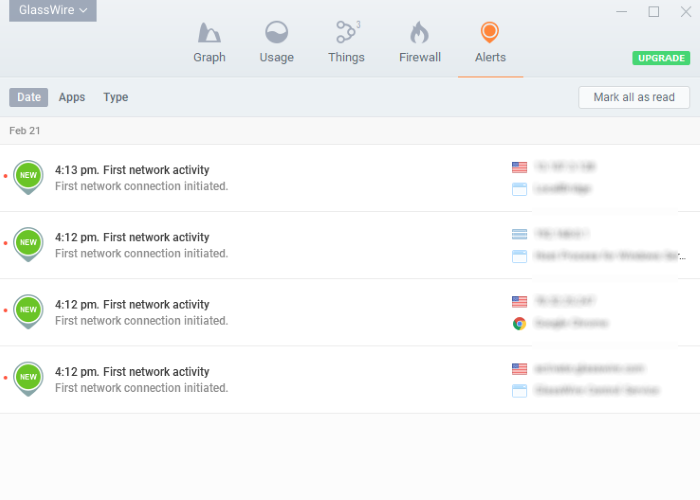
If you have successfully removed Termit ransomware, you know probably think about the ways how to protect your data from future attacks. The best way is to create backups of your data. We recommend you to use only high-quality products. Our choice here is Stellar Data Recovery. This soft can easily create highly-qualified backups, has a user friendly interface and moreover, it can help you to restore your files! Then you should take under strict control all your internet connections. Some of the ransomware viruses connect to various internet services and can even infect computers that are connected to the same local network. That's why it's important to use a strong firewall, that can easily restrict any connection. The best choice is GlassWire. This program has a user friendly interface and it becomes very easy to prevent any ransomware or hacker attack.

To unlock all features and tools, purchase is required ($49.99-$299). By clicking the button you agree to EULA and Privacy Policy.
If you want to learn out more details about the ways how to prevent ransomware attacks, read our detailed article!
Write us an email
If your case is an unusual one, feel free to write us an email. Fill the form below and wait for our response! We will answer you as soon as possible. The files we need to inspect your case are: executable files of the virus, if it's possible; examples of the encrypted files; screenshots of your task manager; ransom note; background screen.
CONCLUSION: nowadays, these solutions are the all possible ways to remove Termit ransomware and decrypt ".[ashtray@outlookpro.net].termit" files. Nowadays the best way to remove it is the Norton 360 . Their specialists improve the scan system and update the databases every day. It helps not only to remove existing problems, but also protects computers from future attacks. If there is a new way to decrypt your files, we will update the article, so stay tuned.