Article’s Guide
- What does .cryptolocker stand for?
- Rapid ransomware encryption process.
- How to remove Rapid Ransomware from your computer
- How to decrypt .cryptolocker files
- Data Recovery
- Automated decryption tools
- Other software
What does .cryptolocker stand for?
A few days ago the one of the most malicious viruses was updated. This virus is called Rapid ransomware and the clearest sign of the infection with it is .cryptolocker extension. The attacks of Rapid ransomware are not predictable. Criminals use various ways to spread it: they can attack the ports of the remote access, they can inject the virus into a fake installator of the software or even send it by email. If we talk about emails, the criminals inject the code of the virus into a harmless file and then send it. This code is executed once the file is opened. In order to increase the chances, that the file will be opened, hackers write fake messages as if they are representatives of a well known company. Since this moment the computer is infected and begins the encryption process. If your computer is already infected with this virus, don’t try to remove Rapid ransomware and decrypt .cryptolocker files manually! Every changing of an encrypted file can damage it without a hope to restore it.
Rapid ransomware encryption process.
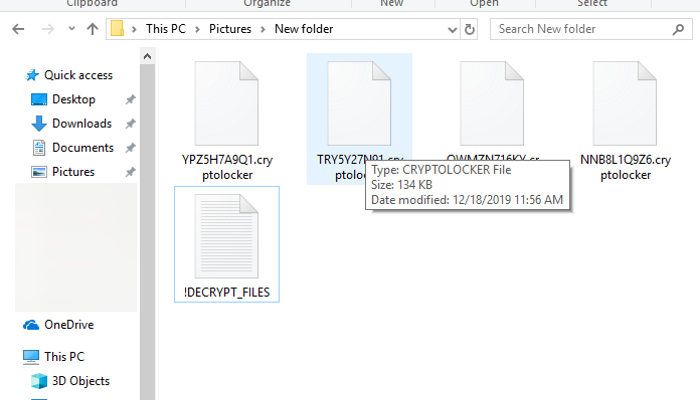
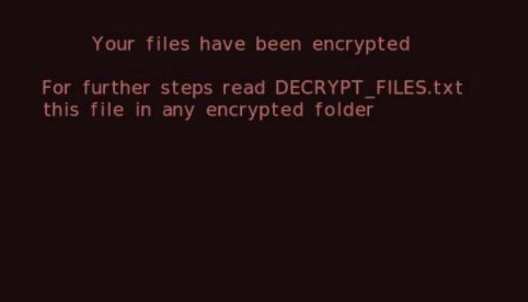
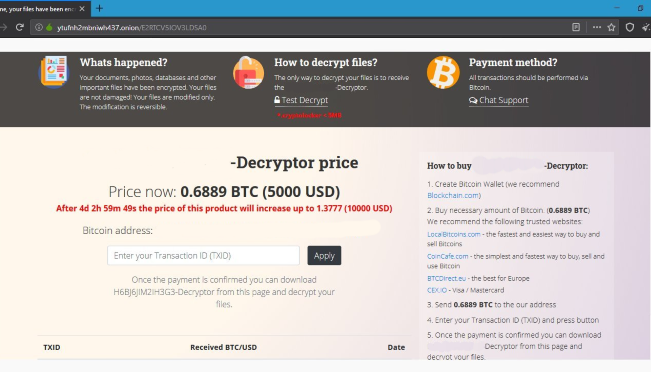
If Rapid ransomware has successfully got into the operating system, it immediately begins the encryption process. It can be divided into two logical steps: the scanning and modifying of files. At first Rapid ransomware looks for the files suitable for the encryption. The suitable files can be of various formats: media files, documents, text files, databases, archives and etc. This process occurs in all folders on the hard drive, so there is a great risk, that operating system files can also be damaged. When it’s done, Rapid ransomware begins to modify the structures of these files and makes them unreadable. As the result, these files get new extensions – .cryptolocker. Moreover, the names of the files are changed randomly. Then the virus changes the background image and creates ransom note – !DECRYPT_FILES.txt. By the means of these messages, the hackers try to assure the victim, that there is no other option, but to pay them. However, no one can give you a guarantee, that they will really help you after the payment. It’s worth mentioning, that Rapid ransomware doesn’t stop to encrypt files and it’s necessary to remove it. As you can see, this situation has nothing in common with a business. They can easily stop all contacts with you after the payment, force you to pay twice, or even destroy all your data. We recommend you to avoid any contact with them and if you really need these files, you can follow our guide on how to remove Rapid ransomware and decrypt .cryptolocker files! Our solutions may be useful for you!
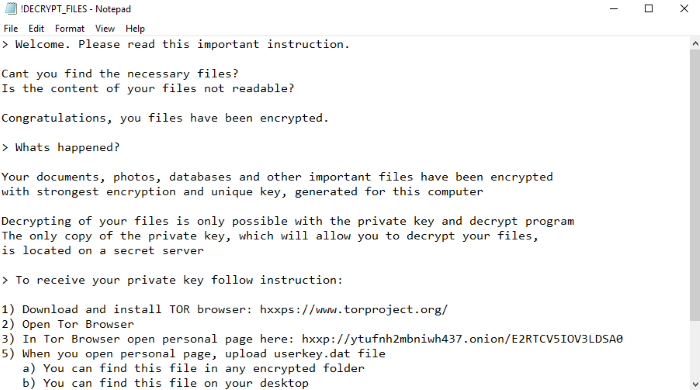
!DECRYPT_FILES.txt
> Welcome. Please read this important instruction.
Cant you find the necessary files?
Is the content of your files not readable?
Congratulations, you files have been encrypted.
> Whats happened?
Your documents, photos, databases and other important files have been encrypted
with strongest encryption and unique key, generated for this computer
Decrypting of your files is only possible with the private key and decrypt program
The only copy of the private key, which will allow you to decrypt your files,
is located on a secret server
> To receive your private key follow instruction:
1) Download and install TOR browser: hxxps://www.torproject.org/
2) Open Tor Browser
3) In Tor Browser open personal page here: hxxp://ytufnh2mbniwh437.onion/E2RTCV5IOV3LDSA0
5) When you open personal page, upload userkey.dat file
a) You can find this file in any encrypted folder
b) You can find this file on your desktop
6) Follow instruction on personal page
Warning: this website is available via Tor Browser only!
Also! At this page you will be able to restore any one file for free!
Your personal-ID: *ID*
How to remove Rapid Ransomware from your computer?
We strongly recommend you to use a powerful anti-malware program that has this threat in its database. It will mitigate the risks of the wrong installation, and will remove Rapid from your computer with all of its leftovers and register files.
Solution for Windows users: our choice is Norton 360 . Norton 360 scans your computer and detects various threats like Rapid, then removes it with all of the related malicious files, folders and registry keys.
If you are Mac user, we advise you to use Combo Cleaner.
How to decrypt “.cryptolocker” files?
Once you’ve removed the virus, you are probably thinking how to decrypt “.cryptolocker” files or at least restore them. Let’s take a look at possible ways of decrypting your data.
Restore “.cryptolocker” files with Data Recovery

- Download and install Data Recovery
- Select drives and folders with your files, then click Scan.
- Choose all the files in a folder, then press on Restore button.
- Manage export location.
The download is an evaluation version for recovering files. To unlock all features and tools, purchase is required ($49.99-299). By clicking the button you agree to EULA and Privacy Policy. Downloading will start automatically.
Decrypt “.cryptolocker” files with other software
Unfortunately, due to the novelty of Rapid ransomware, there are no decryptors that can surely decrypt encrypted files. Still, there is no need to invest in the malicious scheme by paying a ransom. You are able to recover files manually.
You can try to use one of these methods in order to restore your encrypted data manually.
Decrypt .cryptolocker files with Emsisoft decryptor
This software includes information about more than 100 viruses of STOP(DJVU) family and others. All that you need are two files or some luck. You can freely use it as it distributes free of charge. If it doesn’t work for you, you can use another method.