What is Hermes?
Hermes is a name of ransomware-type virus which has nothing to do with the clothing brand. Well, it has already got a bad reputation in the computer world as a dreadful infection. Right after infiltration, virus starts encrypting victim’s files using RSA-2048 asymmetric algorithm. The encryption process takes about two minutes and generally runs without user noticing. In this case, the decryption key is unique for each user, cyber criminals keeps it on remote server being aware of it. Within encryption, this ransomware adds word “HERMES” to the end of the name of all the affected data. For example, myfamily.jpg file turns into myfamilyHERMES.jpg file. Once encrypted, Hermes ransomware creates UNIQUE_ID_DO_NOT_REMOVE file on the desktop. It also places DECRYPT_INFORMATION.html in each folder with the affected files. This file contains instruction on how to pay the ransom for decryption key.
Here is used a typical scheme of all ransomware-type viruses – to force victim to pay them. The only differences of them are the ransom price and encryption method. Cyber criminals state that there are no ways to recover your files but to pay ransom. Once payment is done, they will supposedly send you decryption key. But you should know that nobody can guarantee that they will fulfill their end of the bargain. The practice shows that they are just ignoring people who pays them. That’s why you should not be pushed about by them because you can remain without money and files. On the contrary, you only may encourage them to continue their dirty business. In any case, you will be simply scammed. In order to solve your problem, we prepared this step-by-step guide. First things first, you should remove Hermes ransomware as decryption procedure loses its meaning without this. The best solution to this is to use SpyHunter removal tool which contains Hermes ransomware in its database, so that it will completely wipe out virus from your computer.
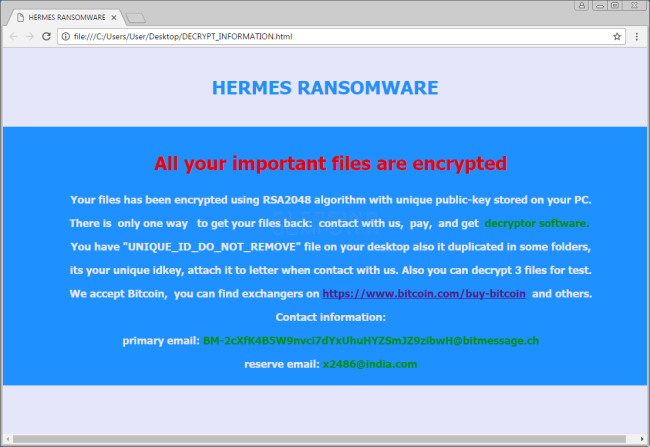
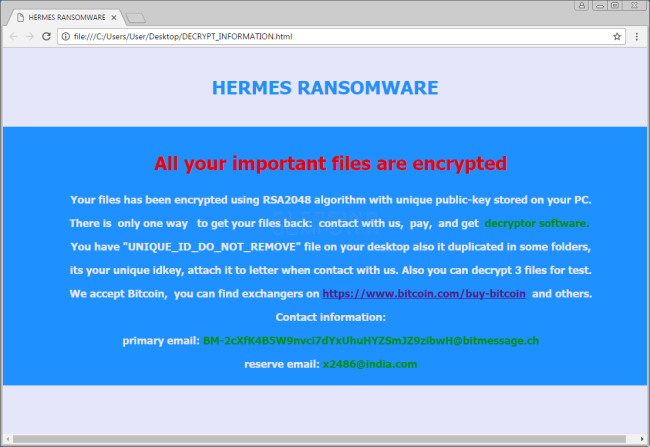
Here’s information you can find in Hermes ransom notes:
All your important files are encrypted Your files has been encrypted using RSA2048 algorithm using unique public-key stored on your PC. There is only one way to get your files back: contact with us, pay, and get decryptor software. You have “UNIQUE_ID_DO_NOT_REMOVE” file on your desktop also it duplicated in some folders, its unique idkey, attach it to letter when contact with us. Also you can decrypt 3 files for test. We accept Bitcoin, you can find exchangers on hxxp://www.bitcoin.com/buy-bitcoin and others. Contact information: primary email: BM-2cXfK4B5W9nvci7dYxUhuHYZSmJZ9zibwH@bitmessage.ch reserve email: x2486@india.com
How Hermes infects your PC?
Like any other ransomware-type viruses, Hermes is distributed primarily through the fraudulent email messages. For example, it might be bill from tax company or online store like Amazon. The virus itself is hided within an attachment. Therefore, be very wary when opening files downloaded from suspicious emails or untrusted sources. Do not rush in these moments since you can compromise your system. The malware is also distributed through fake software updates, torrent (P2P) networks, and trojans as well.
To prevent suсh kinds of the threats as Hermes ransomware in the future follow these tips:
- Adjust your email anti-spam settings to filter out all potentially unsafe incoming messages.
- Make sure, the attachments with the following extensions: .js, .vbs, .docm, .hta, .exe, .cmd, .scr, and .bat. are in the black list
- Rename the vssadmin.exe process to protect Shadow Volume Copies of your files from removal.
- Raise the level of Firewall protection. It can prevent ransomware from connecting with its server.
- Do not forget to backup your files regularly. This will facilitate process of decrypting files in case of infection.
- Install antimalware tool because in most cases, it can detect ransomware in advance and remove the malware before the infection.
How to remove Hermes from your computer?
The best and easiest way to remove Hermes from your computer is to use special anti-malware program that has this threat in its database. As stated above, you need proper and reliable anti-malware program, that’s why we recommend you to use SpyHunter.
It scans your computer and detects various threats like Hermes, then completely removes it. One of the best features of this program – large threat’s database. SpyHunter’s newly advanced ransomware detection technology is able to run an instant ransomware scan and show you a message about detection. After deep scanning of your system, it will easily find and delete Hermes. Use this removal tool to get rid of Hermes for FREE.
How to decrypt files encrypted by Hermes?
Once you’ve removed virus, you are probably thinking of recovering files from encryption. Let’s take a look at possible ways of decrypting your data.
Recover data with Data Recovery

- Download and install Data Recovery
- Select drives and folders with your files, then click Scan.
- Choose all the files in a folder, then press on Restore button.
- Manage export location.
Decrypt encrypted files manually
You can try to use one of these methods in order to restore your encrypted data manually.
Restore data with Windows Previous Versions
This feature is working on Windows Vista (not Home version), Windows 7 and later versions. Windows saves copies of files and folders which you can use to restore data on your computer. In order to restore data from Windows Backup, take following steps:
- Open My Computer and search for the folders you want to restore;
- Right-click on the folder and choose Restore previous versions option;
- The option will show you the list of all the previous copies of the folder;
- Select restore date and the option you need: Open, Copy and Restore.
Restore the system with System Restore
You can always try to use System Restore in order to roll back your system to its condition before infection infiltration. All the Windows versions include this option.
- Type restore in the Search tool;
- Click on the result;
- Choose restore point before the infection infiltration;
- Follow the on-screen instructions.