What does .HRM stand for?
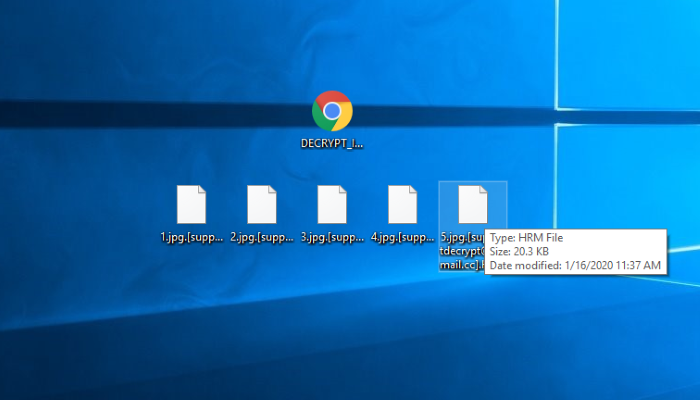
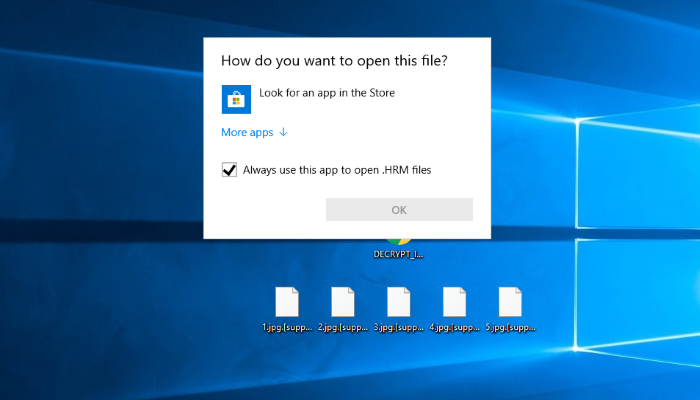
Recently a new threat called Hermes 2.1 has been explored. This virus belongs to file-encryption ransomware group of viruses and as it can be guessed, it locks definite files by the meaning of their modifying. The characteristic feature of the files modified by Hermes 2.1 is .[supportdecrypt@firemail.cc].HRM extension. As the rule, this virus spreads by the means of fake installators and various fake executable files. Such files can be found nearly everywhere and even be sent by email. Moreover, hackers can inject the code of the virus into a common document and send it by email, as if this message comes from a respectful company. The code is executed once such a file has been opened and by the means of various backdoors it injects into the operating system. When it is in, Hermes 2.1 begins to make changes in the Registry in order to make the system think, that Hermes 2.1 is a valid process. Then it infects various system processes in order to avoid various protection systems and creates a great amount of various files. When the preparations are done, Hermes begins to scan all the folders on the hard drive and modifies files, that are suitable for encryption. As the rule, Hermes modifies only media files and documents, however, the virus can be easily upgraded and get the ability to modify executable files and various libraries. As the result of the modification, the files get new extension that has been mentioned above. Then the virus drops the ransom note, that is called DECRYPT_INFORMATION.html. By the means of this note hackers try to assure victims, that the files can be easily restored with the help of a single payment. Unfortunately, the surest way to decrypt the files is to get the decryptor from them, but, in the most cases, they just ignore their victims after the payment or make the situation much worse. That’s why we recommend you to avoid any contact with them. For this purpose we’ve prepared the detailed guide on how to remove Hermes 2.1 ransomware and decrypt .HRM files.
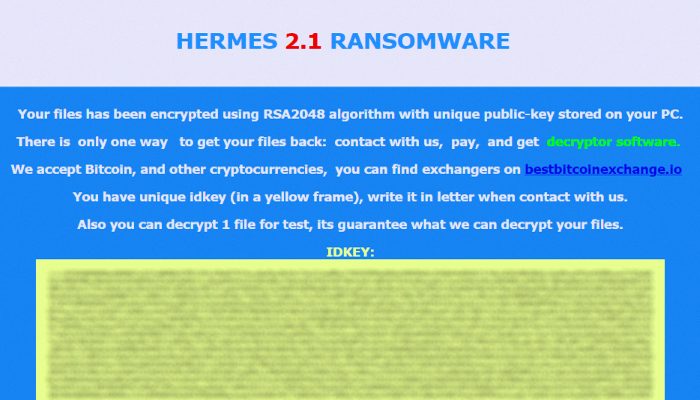
Hermes 2.1 Ransomware
Your files has been encrypted using RSA2048 algorithm with unique public-key stored on your PC.
There is only way to get your files back: contact with us, pay, and get decryptor software.
We accept Bitcoin, and other cryptocurrencies, you can find exchangers on bestbitcoinexchange.io
You have unique idkey (in a yellow frame), write it in letter when contact with us.
Also you can decrypt 1 file for test, its guarantee what we can decrypt your files.
IDKEY:
*Key*
Article’s Guide
- How to remove Hermes 2.1 Ransomware from your computer
- How to decrypt Hermes 2.1 files
- Data Recovery
- Automated decryption tools
- Other software
How to remove Hermes 2.1 Ransomware from your computer?
We strongly recommend you to use a powerful anti-malware program that has this threat in its database. It will mitigate the risks of the wrong installation, and will remove Hermes 2.1 from your computer with all of its leftovers and register files.
Solution for Windows users: our choice is Norton 360 . Norton 360 scans your computer and detects various threats like Hermes 2.1, then removes it with all of the related malicious files, folders and registry keys.
If you are Mac user, we advise you to use Combo Cleaner.
How to decrypt .HRM files?
Once you’ve removed the virus, you are probably thinking how to decrypt .HRM files or at least restore them. Let’s take a look at possible ways of decrypting your data.
Restore .HRM files with Data Recovery

- Download and install Data Recovery
- Select drives and folders with your files, then click Scan.
- Choose all the files in a folder, then press on Restore button.
- Manage export location.
The download is an evaluation version for recovering files. To unlock all features and tools, purchase is required ($49.99-299). By clicking the button you agree to EULA and Privacy Policy. Downloading will start automatically.
Decrypt .HRM files with other software
Unfortunately, due to the novelty of Hermes 2.1 ransomware, there are no decryptors that can surely decrypt encrypted files. Still, there is no need to invest in the malicious scheme by paying a ransom. You are able to recover files manually.
You can try to use one of these methods in order to restore your encrypted data manually.
Decrypt .HRM files with Emsisoft decryptor
This software includes information about more than 100 viruses of STOP(DJVU) family and others. All that you need are two files or some luck. You can freely use it as it distributes free of charge. If it doesn’t work for you, you can use another method.