What is Eris Ransomware?
Eris Ransomware is a cryptovirus that exports user money, encroaching on what is expensive for everyone. Eris encrypts user data of various formats, including office documents, audio, video, multimedia and more. Moreover, Eris assigns the .eris extension to these files, which makes these files simply unreadable and, therefore, unsuitable for use. The main activity of this cryptographer is noticeable at the beginning of July and more and more users complain that their computers are attacked by this. Eris creates a text file called @ READ ME TO RECOVER FILES @.txt. This file contains information about the requirements of scammers and how to decrypt files, although, of course, the main question is how to remove Eris Ransomware and decrypt .eris files. This is what this note looks like:
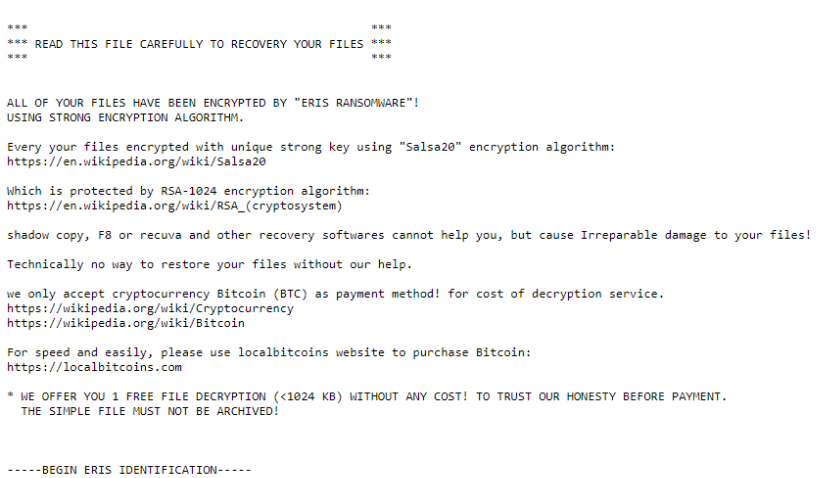
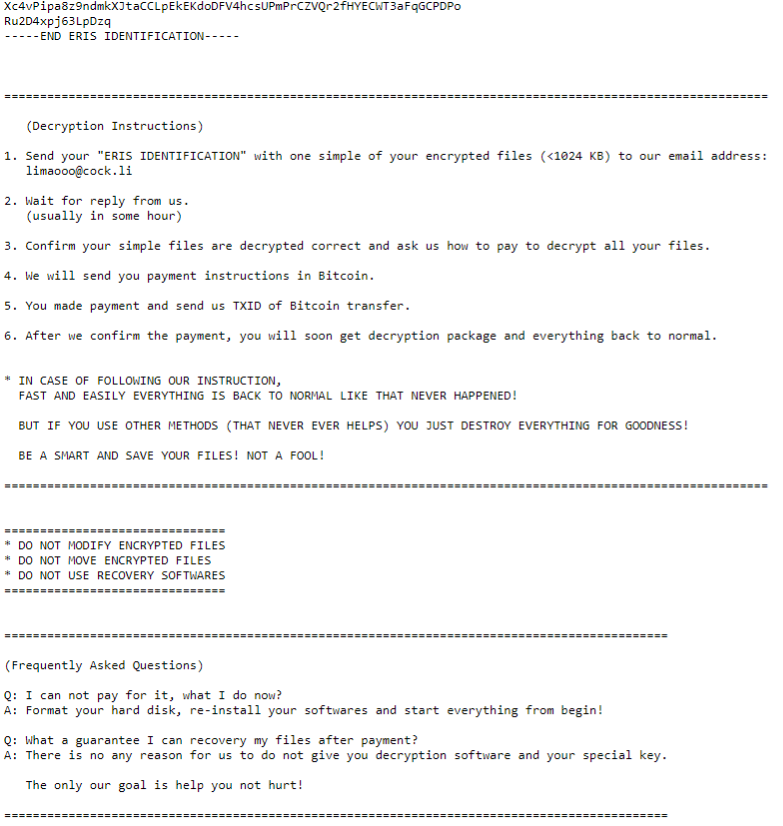
*** *** *** READ THIS FILE CAREFULLY TO RECOVERY YOUR FILES *** *** *** ALL OF YOUR FILES HAVE BEEN ENCRYPTED BY "ERIS RANSOMWARE"! USING STRONG ENCRYPTION ALGORITHM. Every your files encrypted with unique strong key using "Salsa20" encryption algorithm: https://en.wikipedia.org/wiki/Salsa20 Which is protected by RSA-1024 encryption algorithm: https://en.wikipedia.org/wiki/RSA_(cryptosystem) shadow copy, F8 or recuva and other recovery softwares cannot help you, but cause Irreparable damage to your files! Technically no way to restore your files without our help. we only accept cryptocurrency Bitcoin (BTC) as payment method! for cost of decryption service. https://wikipedia.org/wiki/Cryptocurrency https://wikipedia.org/wiki/Bitcoin For speed and easily, please use localbitcoins website to purchase Bitcoin: https://localbitcoins.com * WE OFFER YOU 1 FREE FILE DECRYPTION (<1024 KB) WITHOUT ANY COST! TO TRUST OUR HONESTY BEFORE PAYMENT. THE SIMPLE FILE MUST NOT BE ARCHIVED! -----BEGIN ERIS IDENTIFICATION----- 22deCbsMqoTVKmPJ5UrVqKYNC5ptPwaiCxbcnUqQGfMwnfeKSNb65ui3P63iFtVU iqHBap7sVVsprktGspqZHqVuQiG4XptG9AFWMbBm7gZPr41aLgTxCZsyTVE5cGUr izcB2fL2otEouPEk1Bx799FPxWwsN68uYB6tEdLTkedvcRyuok8331XR1Mh1kR7R ********** -----END ERIS IDENTIFICATION----- ================================================================= (Decryption Instructions) 1. Send your "ERIS IDENTIFICATION" with one simple of your encrypted files (<1024 KB) to our email address: limaooo@cock.li 2. Wait for reply from us. (usually in some hour) 3. Confirm your simple files are decrypted correct and ask us how to pay to decrypt all your files. 4. We will send you payment instructions in Bitcoin. 5. You made payment and send us TXID of Bitcoin transfer. 6. After we confirm the payment, you will soon get decryption package and everything back to normal. * IN CASE OF FOLLOWING OUR INSTRUCTION, FAST AND EASILY EVERYTHING IS BACK TO NORMAL LIKE THAT NEVER HAPPENED! BUT IF YOU USE OTHER METHODS (THAT NEVER EVER HELPS) YOU JUST DESTROY EVERYTHING FOR GOODNESS! BE A SMART AND SAVE YOUR FILES! NOT A FOOL! ================================================================= =============================== * DO NOT MODIFY ENCRYPTED FILES * DO NOT MOVE ENCRYPTED FILES * DO NOT USE RECOVERY SOFTWARES =============================== ================================================================= (Frequently Asked Questions) Q: I can not pay for it, what I do now? A: Format your hard disk, re-install your softwares and start everything from begin! Q: What a guarantee I can recovery my files after payment? A: There is no any reason for us to do not give you decryption software and your special key. The only our goal is help you not hurt! =================================================================
The note says that encryption was performed using several algorithms: AES and Salsa20. Scammers do not talk about the exact cost of the ransom, however, we can safely say that the ransom can reach several thousand dollars in bitcoin equivalent. And, of course, intruders remind the user that any attempt to modify or restore the file on their own can lead to complete loss of information. This is a trick, we recommend you not to pay money. Check out our recommendations to remove Eris Ransomware and decrypt .eris files.
Update: Use following service to identify the version and type of ransomware you were attacked by: ID Ransomware. If you want to decrypt your files, please follow our instruction below or, if you have any difficulties, please contact us: submit@securitystronghold.com. We really can help to decrypt your files.
How to remove Eris from your computer?
You may try to use anti-malware tool to remove Eris ransomware from your computer. Newly advanced ransomware detection technology is able to run an instant ransomware scan, which is perfect to protect your computer in case of a new ransomware attack.
SpyHunter provides an opportunity to remove 1 detected malware for free during trial period. The full version of the program costs $39,99 (you get 6 months of subscription). By clicking the button you agree to EULA and Privacy Policy. Downloading will start automatically.
How to decrypt .Eris files?
Once you’ve removed the virus, you are probably thinking of recovering files from encryption. Let’s take a look at possible ways of decrypting your data.
Recover data with Data Recovery

- Download and install Data Recovery
- Select drives and folders with your files, then click Scan.
- Choose all the files in a folder, then press on Restore button.
- Manage export location.
Restore data with automated decryption tools
Unfortunately, due to the novelty of Eris ransomware, there are no available automatic decryptors for this encryptor yet. Still, there is no need to invest in the malicious scheme by paying a ransom. You are able to recover files manually.
You can try to use one of these methods in order to restore your encrypted data manually.
Restore data with Windows Previous Versions
This feature is working on Windows Vista (not Home version), Windows 7 and later versions. Windows saves copies of files and folders which you can use to restore data on your computer. In order to restore data from Windows Backup, take the following steps:
- Open My Computer and search for the folders you want to restore;
- Right-click on the folder and choose Restore previous versions option;
- The option will show you the list of all the previous copies of the folder;
- Select restore date and the option you need: Open, Copy and Restore.
Restore the system with System Restore
You can always try to use System Restore in order to roll back your system to its condition before infection infiltration. All the Windows versions include this option.
- Type restore in the Search tool;
- Click on the result;
- Choose restore point before the infection infiltration;
- Follow the on-screen instructions.
Written by Rami D