What is ech0raix Ransomware?
Ech0raix belongs to the ransomware family of viruses, to be exact it’s an encryptor. This type of viruses has a very interesting mechanism of infection. First of all it attacks only QNAP NAS devices, as such devices don’t have an integrated security system. Then ech0raix begins to scan your device for your preferable language: it doesn’t attack Russian speaking countries. If your device is a good aim for a hacker, the malware sends to your device a set of commands and then encrypts your files. After encryption process this ransomware adds the appendix .encrypt to your files. Experts tried to prevent the spread of this encryptor by a D.D.O.S. attack, but failed. However, this family of encryptors is well-known, it’s difficult to remove ech0raix, as this modification is new and at the same time it is one of the most widespread encryptors. After encryption process this malware provides you with a ransom note in README_FOR_DECRYPT.txt document:
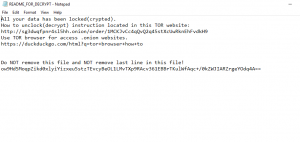
All your data has been locked(crypted).
How to unclock(decrypt) instruction located in this TOR website: http://sg3dwqfpnr4sl5hh.onion/order/12zUXe6TDB5MSW4VJDq5NZv1jVyqA1gC2U
Use TOR browser for access .onion websites.
https://duckduckgo.com/html?q=tor+browser+how+to
Do NOT remove this file and NOT remove last line in this file!
E+Z03/uBSAY26U0eQ/G7QpxQ1KINoBIr7L6Y85LpVv4LaK2VvB8P6O9AxXqAR7eDDbFgvFxkyz1XVP+iyoOQ/w==
We don’t recommend you to open these links. Moreover, we advise you not to pay hackers a cent, as you don’t have any guarantee that they will honor their promises. If you want to remove ech0raix Ransomware and decrypt .encrypt files, you may be interested in our guide.
Article’s Guide
- How to remove ech0raix Ransomware from your computer
- How to remove ech0raix Ransomware encryption from your files
- Data Recovery
- Automated decryption tools
- Windows Previous Versions
How to remove ech0raix Ransomware from your computer?
We strongly recommend you to use a powerful anti-malware program that has this threat in its database. It will mitigate the risks of the wrong installation, and will remove FTCODE from your computer with all of its leftovers and register files.
Solution for Windows users: our choice is Norton 360 . Norton 360 scans your computer and detects various threats like FTCODE, then removes it with all of the related malicious files, folders and registry keys.
If you are Mac user, we advise you to use Combo Cleaner.
How to remove ech0raix Ransomware encryption from your files?
Once you’ve removed the virus, you are probably thinking of recovering files from encryption. Let’s take a look at possible ways of decrypting your data.
Recover data with Data Recovery

- Download and install Data Recovery
- Select drives and folders with your files, then click Scan.
- Choose all the files in a folder, then press on Restore button.
- Manage export location.
Restore data with automated decryption tools
Unfortunately, due to the novelty of ech0raix ransomware, there are no available automatic decryptors for this encryptor yet. Still, there is no need to invest in the malicious scheme by paying a ransom. You are able to recover files manually.
You can try to use one of these methods in order to restore your encrypted data manually.
Restore data with Windows Previous Versions
This feature is working on Windows Vista (not Home version), Windows 7 and later versions. Windows keeps copies of files and folders which you can use to restore data on your computer. In order to restore data from Windows Backup, take the following steps:
- Open My Computer and search for the folders you want to restore;
- Right-click on the folder and choose Restore previous versions option;
- The option will show you the list of all the previous copies of the folder;
- Select restore date and the option you need: Open, Copy and Restore.
Restore the system with System Restore
You can always try to use System Restore in order to roll back your system to its condition before infection infiltration. All the Windows versions include this option.
- Type restore in the Search tool;
- Click on the result;
- Choose restore point before the infection infiltration;
- Follow the on-screen instructions.